Everybody in the 21st century wants to earn money, in both real and virtual form. Now, sites like bitcoinsrush.com help people earn a lot of cryptocurrency. Unfortunately, a section of people is ever ready to steal the hard-earned money of others. It is where cryptojacking comes in.
Cryptojacking is the process of utilizing the computer of another person for mining cryptocurrency. The process is illegal and those who indulge in it are known as hackers.
Cryptojacking may be of three types:
- Browser-based
- Cloud-based
- File-based
The cryptojackers download malware to execute the crypto-mining scripts, access the cloud services and hijack the IT infrastructure. Hence, it is the combined responsibility of IT professionals and the employees of an organization to combat cryptojacking.
How cryptojacking works?

It is important to know how cryptojacking works, so that the potential victims can stay alert.
Executing a script for crypto mining:
Cybercriminals embed a crypto mining code for compromising some assets. After that, they wait so that a victim unknowingly executes that script. This happens when either they browse through a website that contains infected ads or they click on a link or an attachment. It helps in running the crypto-mining script. The crypto mining script continues to run in the background, after its execution. The users are not aware of it.
Solution of Algorithms
All scripts take the help from some device where they solve complicated algorithms. They help to mine something known as “block.” These blocks add up to form something known as a block chain. A block chain may be described as a technology that saves virtual info regarding bitcoins..
Cryptojackers get rewarded:

Any time the cryptojackers include a brand new block to the blockchain, they get virtual coins, as rewards. They may put these cryptocurrency coins directly in their e-wallets, anonymously. They earn these virtual coins in return of low threat and risk.
Points for preventing cryptojacking:
We find it difficult to find out when the cyber criminals have hacked an account. However, people may follow a few general tips, to prevent cryptojacking and protect their crypto-assets.
The tips are as follows:
Have a competent technical team:
Organizations should have a qualified technical team. All members of the IT department require special training so that they may diagnose cryptojacking. They must have the capacity to identify any initial sign hinting towards cryprojacking. Then, they have to adopt instant steps for combating it at the beginning.
Make use of An Extensions:

Cryptojackers often place a hacking system in browsers. Hence, people should utilize browser extensions for blocking them throughout the web. Anti-Miner and No-Coin are classic examples of anti-crypto mining extensions.
Utilize Ad-Blocking features
Hackers often embed a Cryptojacking script in online advertisements. Any ad-blocker may identify as well as close harmful cryptomining codes.
Educating the employees of an organization:
The IT people often depend on the workers to keep them posted at a time the systems get too hot or run at a low speed.. The workers require extensive training in cyber security. Modules informing them not to try opening a link which comes through emails. It should become an integral part of cyber security lessons.
The employees should know that the links from unknown email ids may execute some cryptocurrency codes. They should just download from trustworthy links. A similar law should apply for their personal emails.
Disabling

It is a good idea to disable JavaScript while browsing online. This step is helpful in preventing the cryptojacking codes against corrupting a system. Professional computer users complain that blocking JavaScript while browsing through the net may ban many necessary activities. However, all the organizations are required to stay careful as well as safe to counteract cryptojacking.
The steps to identify Cryptojacking:
People claim that identifying the systems which get affected through cryptojacking become difficult to identify. It may destroy the whole business of a company. A code which is used in cryptomining scripts does not allow itself to be detected. It calls for extra vigilance from the IT team. A few tips may help people identify cryptojacking and prevent it from spreading, before it is too late. The tips are as follows:
Check utility of CPU:
The IT team needs to track the use of CPU. The owners of CPU may do it themselves with some help from Task Manager or Activity Monitor. In case an user is browsing through a website that contains very less or no media content, but the CPU is getting used excessively, it indicates that cryptomining scripts have to remain active.
Fall in Performance:
A system may provide awesome performance. Its stellar performance decreases when cryptojacking occurs. The employees should report the decreased processing of their desktop or laptop to the IT department immediately.
Overheated:
Cryptojacking is a resourceful project. It either damages the computer or reduces its lifespan. The fans within the devices work for an unnecessarily long time. for the sake of cooling the ice. It might end up with the system getting damaged.
Scanning for Malware:

Many malware may be specially made for this phenomenon. They utilize their individual resources like cryptojacking scripts. Such malware may encrypt the files, keep the files as a ransom to acquire virtual currency or damage a system. Hence, it is a good idea to utilize a security-based software to scan for malware. Regular scanning will cooperate in identifying harmful scripts. Software like PowerShell is helpful to detecting an onslaught of cryptojacking.
Stay updated about the recent fashion of Cyptojacking:
Cybercriminals frequently modify code. They often produce updated methods of delivery for embedding the latest scripts on the system of the computer. So, the users should proactively stay updated about the recent trends. Such updated knowledge will help them identify this on the devices and network.
Monitoring Websites:
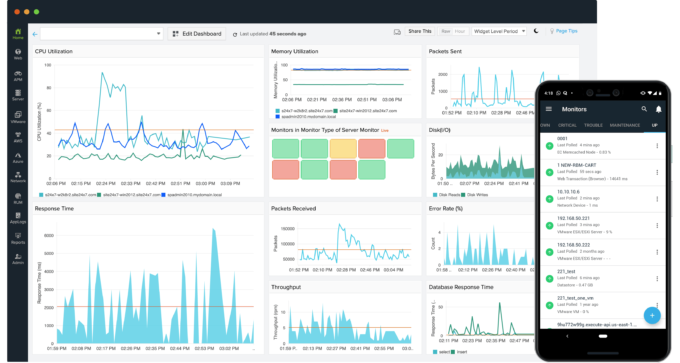
Cybercriminals are always on the lookout for systems which allow them to embed the cryptojacking code. To counter that, the computer owners should monitor the websites. They should scrutinize for even the minute alterations to our files or online pages. If any of any cryptojacking code is identified soon, it may prevent further damage.
Conclusion:
Cryptojacking is deemed illegal. So, people should be vigilant against cryptojacking affecting the level of their performance. Veteran IT professionals warn that cryptojacking has the capability to ruin the entire business operations of an organization.